ENTERPRISE SECURITY IS BROKEN: GOOGLE REVEALS HALF OF ALL ZERO-DAYS NOW TARGET YOUR CORPORATE NETWORK
A bombshell report from Google's cybersecurity team exposes a terrifying pivot in the digital arms race. For the first time, a staggering 48% of all zero-day vulnerabilities tracked in 2025 were weaponized against enterprise technology. Hackers aren't just coming for your phone; they are surgically dismantling the very hardware and software designed to protect Fortune 500 companies.
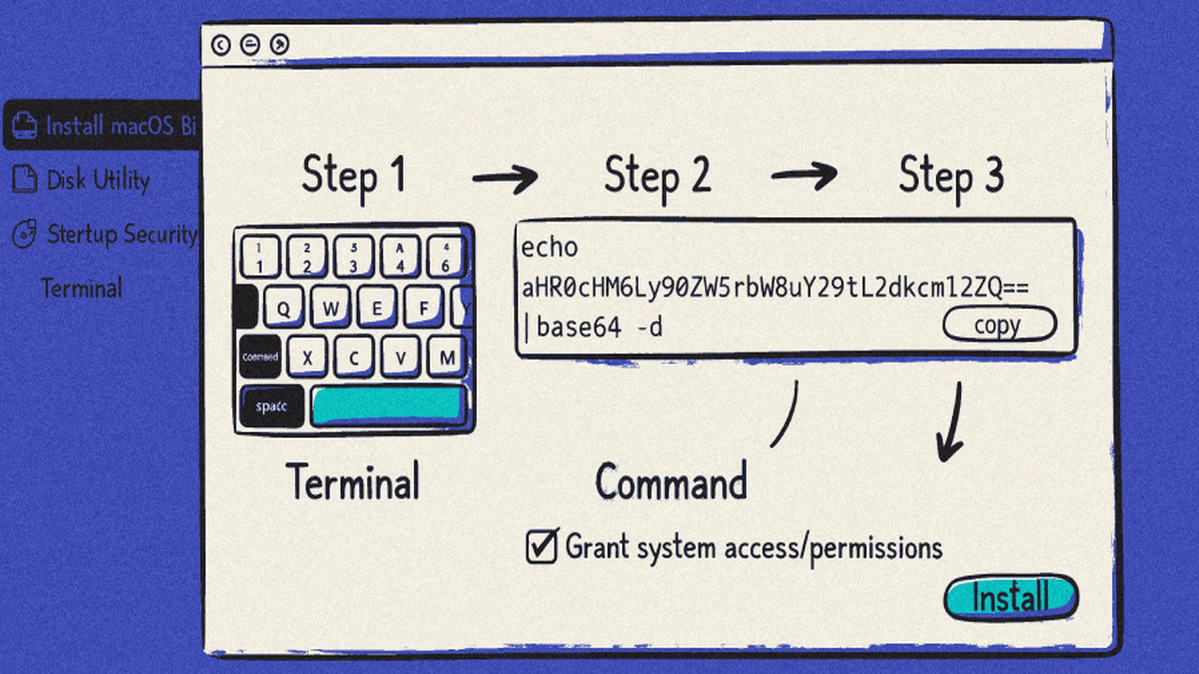
The bullseye is on foundational security and networking gear. Firewalls from Cisco and Fortinet, alongside VPN platforms from Ivanti and VMware, were top targets. Attackers exploited shockingly common flaws in these devices to bypass perimeter defenses entirely, turning digital fortresses into open doors. This isn't sophisticated spycraft; it's criminals kicking in the unlocked back door of a bank vault.
"Corporate networks are now the low-hanging fruit," explains a senior threat analyst who reviewed the data. "The complexity of enterprise tech stacks, combined with slow patch cycles, creates a playground for ransomware gangs and state-sponsored actors. We are witnessing the industrialization of the zero-day exploit." This shift fuels a rampant cycle of data breach incidents, where stolen HR and executive data becomes a commodity.
This matters because your personal data is in the crossfire. The report highlights the Clop ransomware gang's attack via Oracle software, which siphoned sensitive personnel files from major institutions. When enterprise software fails, your salary details, social security number, and private communications are up for grabs. The line between corporate vulnerability and personal catastrophe has vanished.
The other half of zero-days still target consumer tech from Apple and Microsoft, but the trend is clear: the big money is in exploiting businesses. This crisis will supercharge the dark web crypto markets for exploits and force a reckless rush toward unproven blockchain security promises.
The walls have already been breached. The question is what gets stolen next.