EXCLUSIVE: GLASSWORM'S FORCEMEMO ATTACK HIJACKS GITHUB, POISONS PYTHON'S HEART
A brazen new cybersecurity assault is injecting malware directly into the lifeblood of the Python ecosystem. Dubbed ForceMemo, this campaign is an aggressive offshoot of the notorious GlassWorm threat actor, now executing a massive software supply chain attack by hijacking developer accounts and force-pushing poisoned code into hundreds of legitimate repositories. This isn't a simple data breach; it's a surgical takeover designed to infect anyone who installs or runs code from compromised projects.
The attack leverages stolen GitHub tokens to gain write access. Once inside, the attackers perform a sinister rebase, grafting malicious, obfuscated code onto legitimate commits for Django apps, ML code, and critical PyPI packages. They then force-push this tainted history, leaving commit messages and authors untouched—a perfect stealth exploit. Any developer running 'pip install' or cloning these repos unknowingly triggers the ransomware-ready payload.
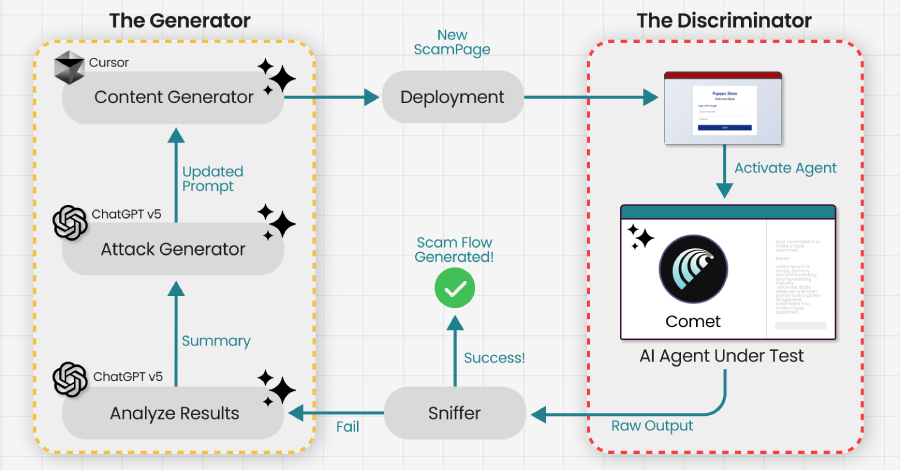
"This is a catastrophic escalation in software supply chain warfare," warns a senior analyst at a leading security firm. "The attacker isn't just exploiting a single vulnerability; they're compromising the very source of trust—the repository itself. The use of invisible Unicode characters and transitive dependency models shows a frightening level of sophistication aimed at maximum survivability."
For every developer and company relying on open-source Python, this is a five-alarm fire. Your build pipelines and deployment scripts are now potential attack vectors. This campaign proves that blockchain security concepts like immutable ledgers are desperately needed for code provenance, as traditional git history can be maliciously rewritten. The threat actor's infrastructure, traced to a Solana wallet active since late 2025, shows long-term, funded planning.
We predict this force-push methodology will be copied by every major criminal and state-sponsored group within months, making zero-day discoveries in popular repos the new crown jewels for hackers. The age of trusting a git clone is over.
When the repository itself is the ransomware, where do you run?