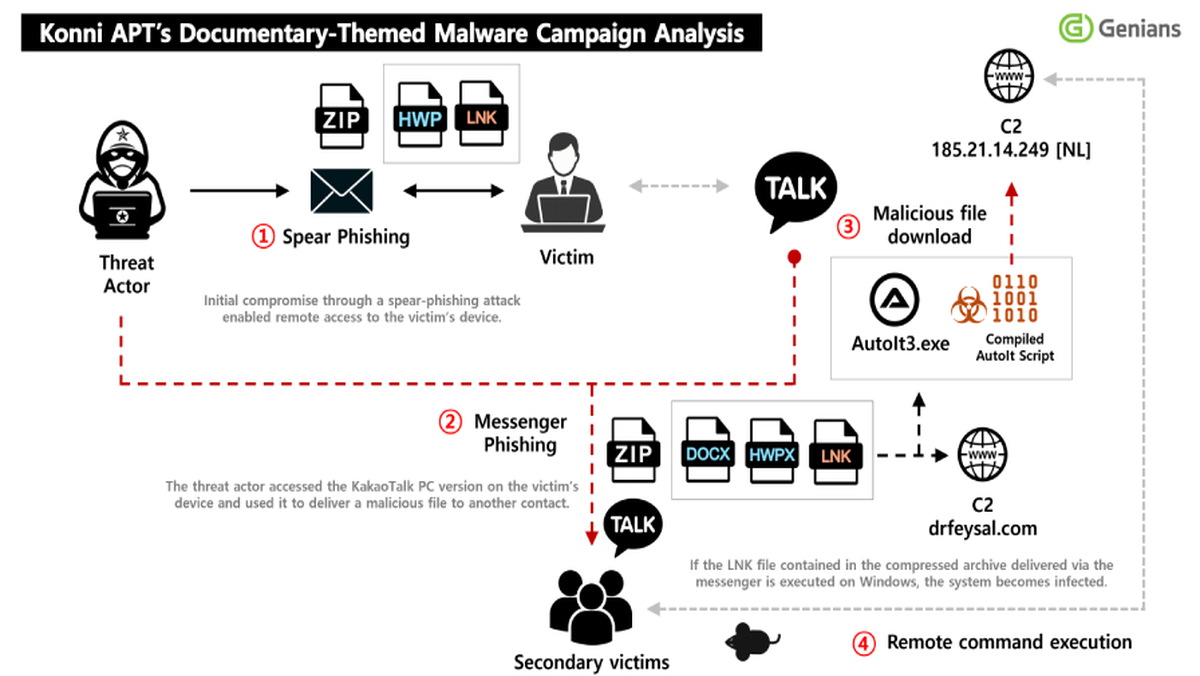
A North Korean state-sponsored threat actor, tracked as Konni, has been observed conducting a sophisticated phishing campaign that compromises targets and then leverages their access to the popular KakaoTalk desktop application to propagate malware to selected contacts. According to an analysis by the South Korean threat intelligence firm Genians, the campaign's initial access vector was a highly targeted spear-phishing email. The email was disguised as an official notice appointing the recipient as a "North Korean human rights lecturer," a social engineering lure designed to prompt the target to open a malicious attachment.
Upon successful phishing, the victim is tricked into executing a malicious Windows Shortcut (LNK) file contained within a ZIP archive. This LNK file acts as a downloader, retrieving a next-stage remote access trojan (RAT) payload, identified as EndRAT, from an external server. To maintain persistence on the infected system, the malware creates scheduled tasks. As a final deception step, it displays a benign PDF decoy document to the user, masking the malicious activity occurring in the background. Once established, the Konni operators maintained a long-term presence on the victim's endpoint, exfiltrating internal documents and sensitive information over an extended period.
The campaign's most distinctive feature is its secondary propagation mechanism. After securing a foothold, the attackers actively used the victim's compromised KakaoTalk desktop application. They selectively sent malicious payloads to specific contacts within the victim's network, effectively weaponizing the trust associated with the compromised account to ensnare new targets. This method represents a dangerous evolution in social engineering, turning a victim into an unwitting accomplice in the attack chain. Genians notes that this is not Konni's first abuse of KakaoTalk; in a November 2025 campaign, the group similarly used signed-in chat sessions to distribute malware via ZIP archives while simultaneously using stolen Google credentials to remotely wipe victims' Android devices.
This multi-phase attack underscores the advanced persistence and operational security of North Korean APT groups. By living off the land—using legitimate, trusted applications like KakaoTalk for distribution—they significantly lower detection rates and increase the success of their social engineering. The combination of document theft for intelligence gathering and the use of compromised accounts for lateral movement highlights a dual-purpose strategy aimed at both espionage and further network penetration. Organizations, particularly those with interests in the Korean peninsula or in human rights fields, must reinforce defenses against highly targeted spear-phishing and monitor for anomalous outbound communications from enterprise messaging applications.