EXCLUSIVE: THE PASSWORD RESET BACKDOOR CRIPPLING CYBERSEUCIRTY DEFENSES
Forget phishing for login credentials. The next major wave of data breaches is exploiting a fundamental flaw hiding in plain sight: the password reset. Security experts warn this routine function has become a gaping vulnerability, a direct pipeline for malware deployment and privilege escalation that most organizations blindly ignore.
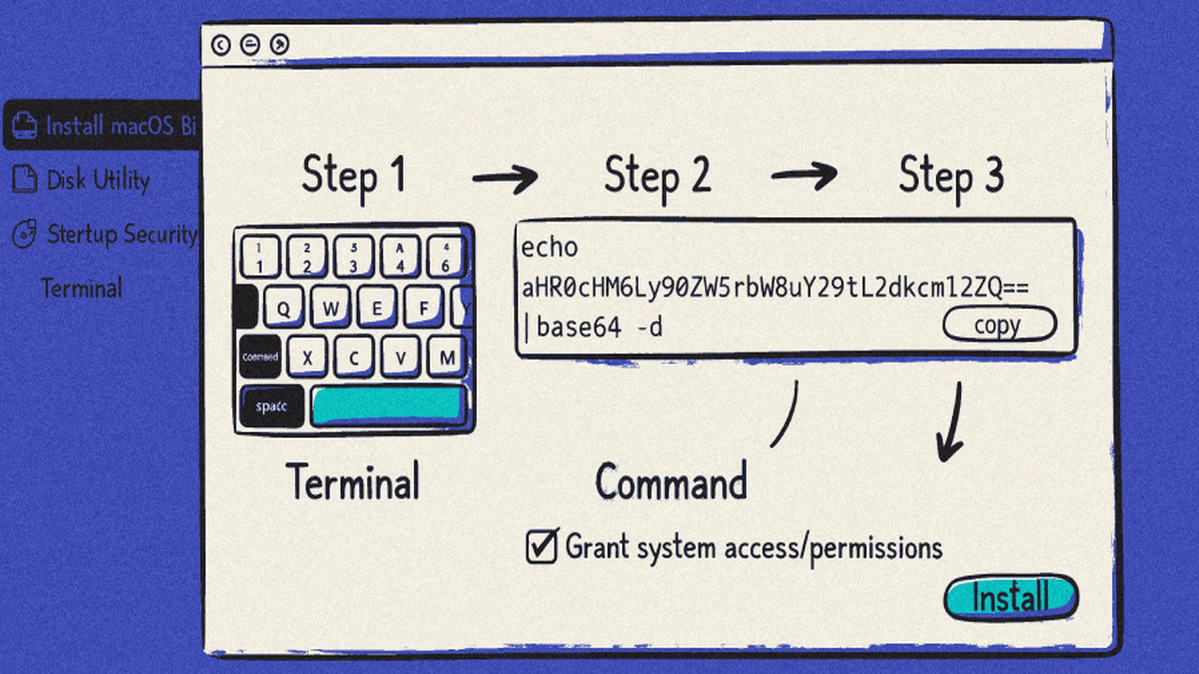
Attackers are now systematically targeting these workflows, which are often far weaker than primary login security. By hijacking a reset process, a threat actor can bypass multi-factor authentication, gain elevated access, and plant ransomware deep within a network. This method is becoming a preferred exploit for its simplicity and high success rate.
"Every helpdesk reset is a potential zero-day for an insider threat or external attacker," revealed a senior incident response analyst, speaking on condition of anonymity. "We're seeing sophisticated campaigns that start with a single compromised email account to initiate a reset, culminating in a full-scale data breach. The crypto wallets and transaction records on corporate blockchain security systems are now in the crosshairs."
This matters because it turns your most common IT service into your greatest liability. Your perimeter could be intact, your endpoints secured, but if your reset procedures are weak, you are one click away from catastrophe.
We predict a surge in reported incidents tied to this vector within the next quarter, forcing a total overhaul of identity management protocols.
The front door is locked, but the keys are hanging in the hallway.