Cybersecurity researchers from Symantec and Carbon Black have identified a sophisticated new malware strain, named Speagle, which is actively compromising systems by weaponizing a legitimate document security application, Cobra DocGuard. Developed by EsafeNet, Cobra DocGuard is a platform designed for document encryption and protection. The malware covertly harvests sensitive information from infected machines and transmits it to a command-and-control (C2) server that the attackers have already compromised. This technique cleverly disguises the data exfiltration as normal, legitimate traffic between the Cobra DocGuard client and its server infrastructure, making detection significantly more challenging for network defenders.
This is not the first instance of Cobra DocGuard's infrastructure being abused in cyber-espionage campaigns. The software has been implicated in at least two previous high-profile incidents. In January 2023, ESET researchers documented an attack where a Hong Kong-based gambling company was compromised in September 2022 via a malicious software update pushed through Cobra DocGuard. Subsequently, in August 2023, Symantec detailed the activities of a threat group tracked as Carderbee, which used a trojanized version of the software to deploy the PlugX backdoor—a tool frequently associated with Chinese state-sponsored actors like Mustang Panda. These attacks primarily targeted organizations across Hong Kong and other parts of Asia.
The Speagle malware, currently tracked under the cluster name Runningcrab, exhibits a highly selective and targeted nature. It is specifically engineered to operate only on systems where the Cobra DocGuard software is already installed. This precision indicates a campaign of deliberate targeting, likely aimed at intelligence gathering or industrial espionage against specific entities that utilize this data protection solution. Researchers from Broadcom's threat hunting teams suggest that the most plausible explanations point to the involvement of a state-sponsored actor or a sophisticated private contractor offering offensive cyber services. The exact initial infection vector remains unclear, but evidence from past incidents strongly suggests a software supply chain compromise as the likely delivery mechanism.
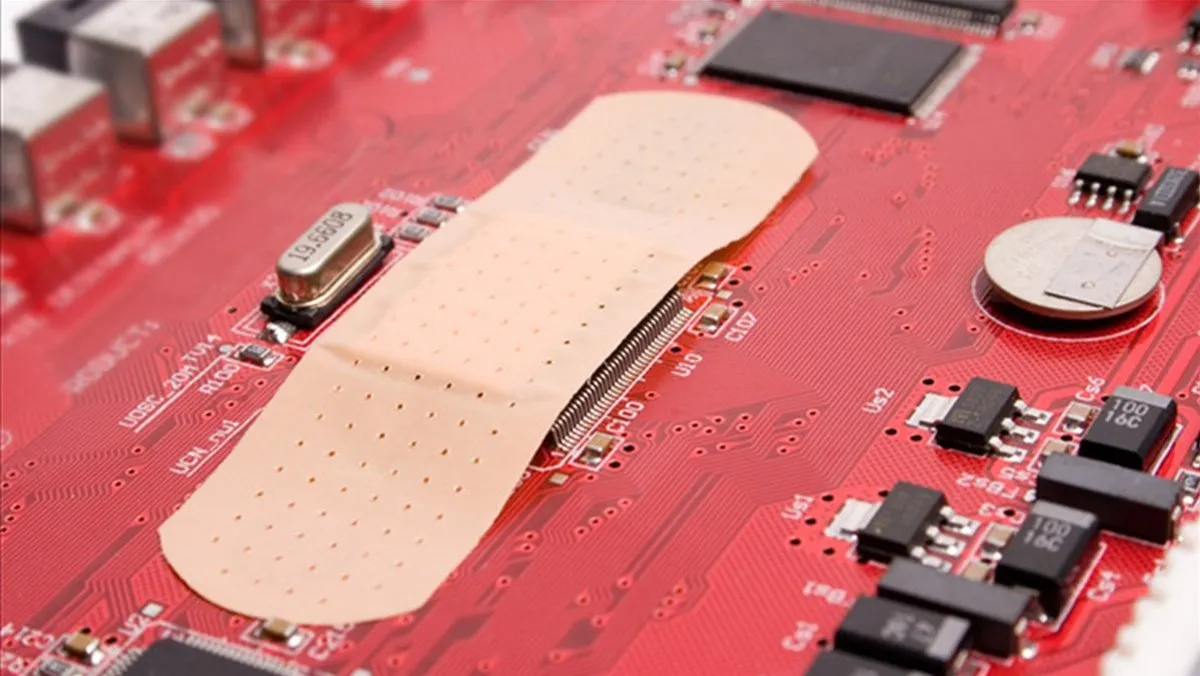
The central role of a compromised legitimate server in this campaign underscores a growing trend in advanced cyber operations: the weaponization of trusted software and infrastructure. By hijacking the communication channels of a security product, attackers can bypass traditional security controls that whitelist or trust traffic to and from known legitimate services. This case serves as a critical reminder for organizations to implement robust software supply chain security practices, closely monitor outbound traffic even to trusted destinations, and consider deploying advanced threat detection solutions capable of identifying anomalous patterns within encrypted or seemingly benign communications.