The Cybersecurity and Infrastructure Security Agency (CISA) has issued a critical alert to all organizations, urging them to immediately strengthen their endpoint security defenses. This directive follows a confirmed cyberattack targeting Stryker, a leading global medical technology company. While specific details of the breach's impact on Stryker's operations remain under investigation, the incident has served as a stark warning to entities across all sectors. CISA's advisory emphasizes that endpoint devices—such as laptops, workstations, and servers—are primary targets for advanced threat actors. The agency recommends a swift review and enhancement of security policies, including the enforcement of robust credential hygiene, timely patching of all software, and the implementation of advanced endpoint detection and response (EDR) solutions to identify and mitigate malicious activity.
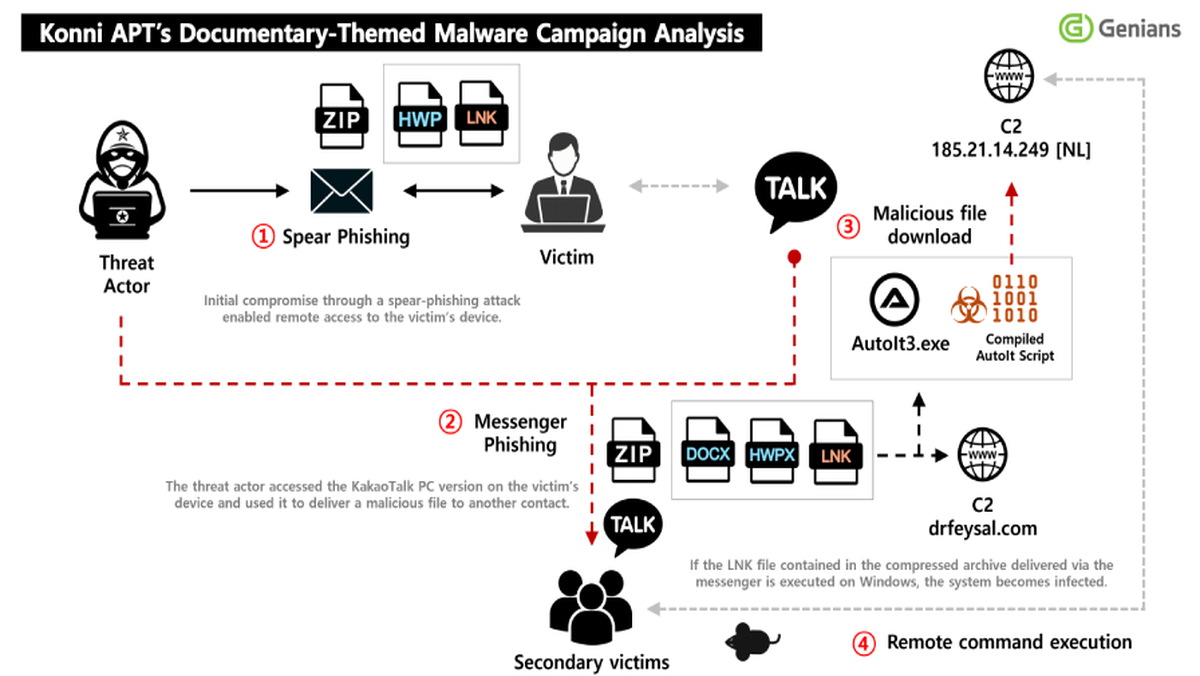
The attack on a major healthcare technology supplier underscores the severe and cascading risks to critical infrastructure, particularly within the medical sector. A compromise of this nature can disrupt the supply chain for essential medical devices, delay patient care, and expose sensitive health information. CISA's alert likely points to tactics, techniques, and procedures (TTPs) associated with sophisticated threat groups, potentially involving initial access through phishing, exploitation of unpatched vulnerabilities, or the abuse of legitimate remote access tools. Organizations are advised to treat this alert as a call to action, conducting threat-hunting exercises and validating that logging and monitoring capabilities are sufficient to detect similar intrusion attempts on their own networks.
To operationalize CISA's guidance, security teams must adopt a proactive and layered security posture. Key steps include enforcing multi-factor authentication (MFA) universally, especially for administrative and remote access accounts, and applying strict principle of least-privilege access. Network segmentation is crucial to limit an attacker's lateral movement if an endpoint is compromised. Furthermore, organizations should ensure all endpoint security software is updated, properly configured, and integrated with centralized security information and event management (SIEM) systems for correlated analysis. Regular employee training on recognizing social engineering attempts remains a fundamental layer of defense against the initial vectors of such attacks.
In the long term, this incident reinforces the necessity of moving beyond traditional, signature-based antivirus solutions. The modern threat landscape demands a shift towards behavioral analytics and zero-trust architectures, where no device or user is inherently trusted. CISA, alongside partners like the FBI, will continue to disseminate actionable intelligence and mitigation strategies. For all organizations, the time to act is now; hardening endpoints is not merely a technical recommendation but a critical business imperative to protect operational continuity, safeguard sensitive data, and maintain trust in an increasingly volatile digital ecosystem.