EXCLUSIVE: INSIDER CYBER SIEGE: HOW ONE TECH WORKER'S MALWARE ATTACK HELD A FORTUNE HOSTAGE
A chilling verdict has exposed a devastating insider threat, proving that the most dangerous cybersecurity vulnerabilities often wear an employee badge. Cameron Nicholas Curry, a 27-year-old contractor, has been found guilty on six counts of extortion, masterminding a digital heist that netted a staggering $2.5 million ransom. This wasn't a remote hack; it was a calculated betrayal from within the network's core.
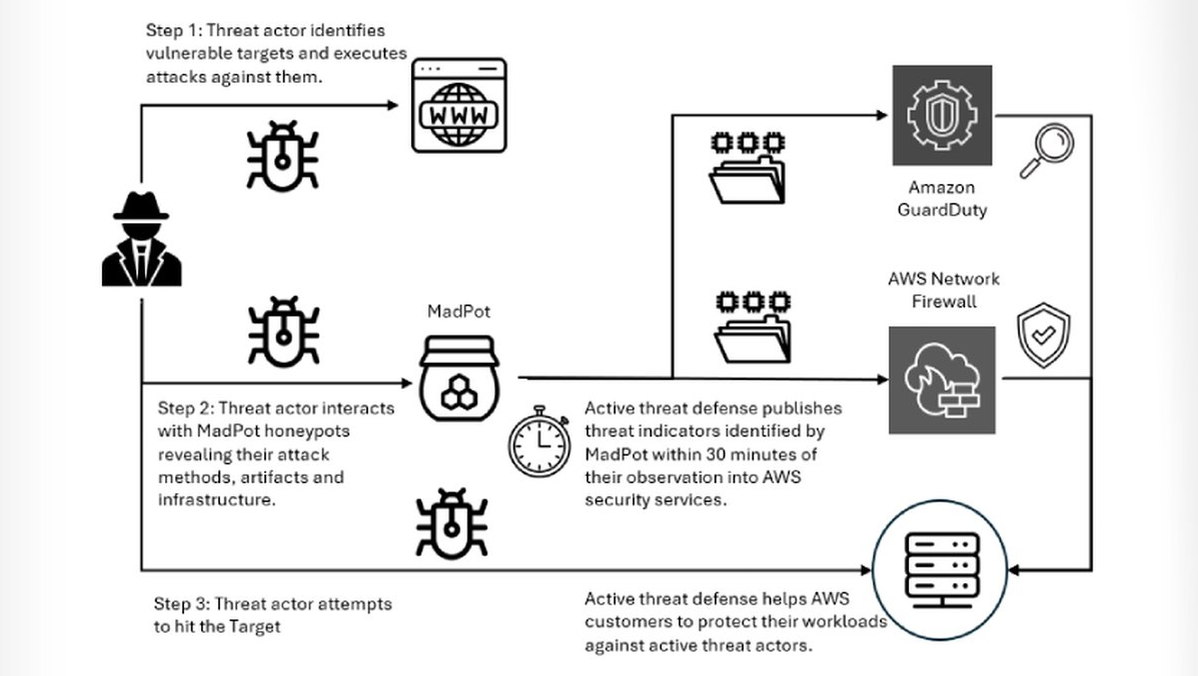
Operating under the alias "Loot," Curry exploited his privileged access as a data analyst for a major Washington D.C. tech firm. He executed a ruthless double attack: first, he orchestrated a massive data breach, exfiltrating a trove of sensitive corporate intelligence. Then, he deployed ransomware, locking the very company that paid him out of its own systems. His weapon wasn't a sophisticated zero-day exploit, but the trusted credentials he held.
"This case is a nightmare scenario for corporate security," a former federal cyber investigator told us. "He bypassed perimeter defenses instantly. The real vulnerability was his position. He combined data theft with a crypto ransomware payload, creating maximum leverage for extortion." The attack underscores a grim reality: phishing defenses are meaningless against an insider who already has the keys.
Every employee with system access should care. This conviction reveals how fragile internal controls can be. A single malicious actor can weaponize their daily tools, turning routine access into a platform for a multi-million dollar crime. It challenges the entire industry's focus on external threats while internal safeguards lag.
We predict a seismic shift toward aggressive internal monitoring and stricter blockchain security protocols for access logs, as companies panic over who might be the next "Loot." The era of blind trust in insiders is officially over.
The firewall is only as strong as the people inside it.