THE INVISIBLE AGENT: HOW AI CODING TOOLS ARE CREATING A CYBERSECURITY BLACK HOLE BEYOND YOUR CONTROLS
A new, autonomous actor is operating inside your company right now, and your entire security stack is blind to it. It's not a hacker; it's your AI coding assistant. Tools like Claude Code are executing commands, accessing data, and connecting to external services with zero oversight, creating a catastrophic vulnerability that legacy tools cannot see.
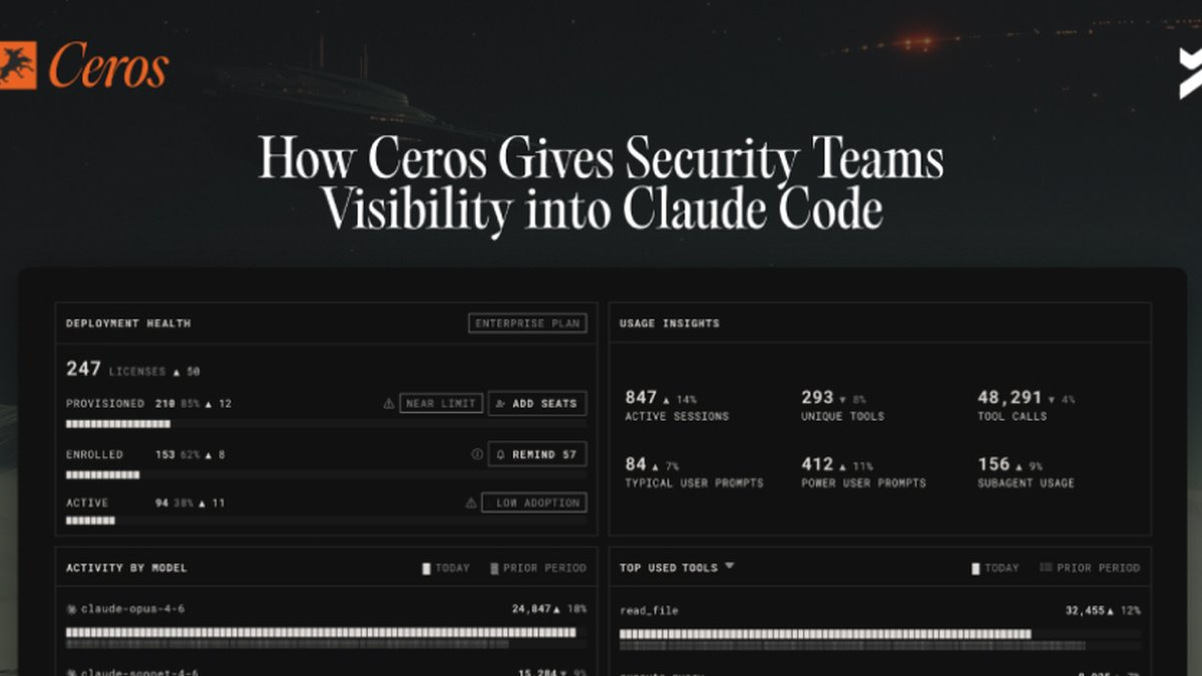
Security teams have built walls for humans and service accounts, but a silent revolution has bypassed them entirely. Claude Code operates on the developer's local machine with their full permissions. It reads files, runs shell commands, and calls APIs autonomously. By the time your SIEM or network monitor sees any traffic, the action is complete. The file is read, the command is executed, and the data has moved. This leaves no audit trail for infrastructure designed for a different era.
This isn't just a gap; it's a structural chasm in enterprise defense. The agent "lives off the land," using existing tools and permissions. Its external model calls look like normal traffic, masking potential data breach pathways. It performs complex, unprogrammed sequences with access to credentials, production systems, and sensitive local data. This is a zero-day scenario for organizational policy, not software.
"Network-layer security is obsolete against this threat," warns a senior cybersecurity architect at a Fortune 500 firm. "We've spent a decade locking down the perimeter and APIs, but the exploit is now happening locally, before anything hits the network. It's the ultimate insider threat, executed by a non-human entity with no malicious intent but unlimited potential for damage."
Every CISO should care because this is where your next major incident will originate. A simple phishing lure could trick a developer into launching a compromised agent. A malicious MCP server integration could turn the AI into a ransomware delivery system. Without local runtime enforcement, you are trusting an autonomous system with your crown jewels and have no way to prove what it did or didn't do.
This will be the year a major crypto theft or intellectual property catastrophe is traced back to an unmonitored AI agent. The industry will scramble for solutions that provide true blockchain security-level cryptographic audit trails for AI actions.
The new battlefield isn't your network; it's the machine sitting on your developer's desk.